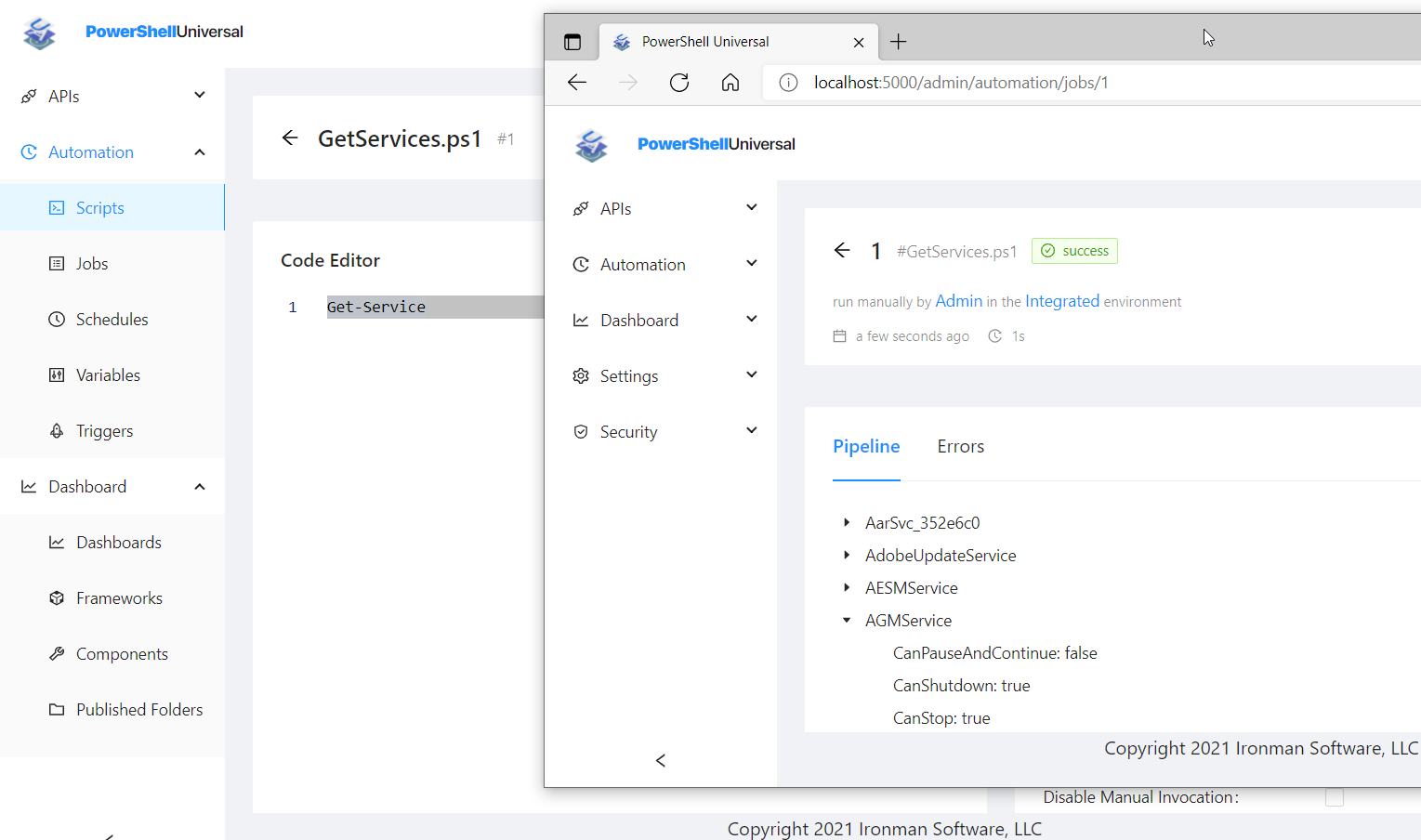
Take your PowerShell skills to the next level with PowerShell Universal. Create robust web applications that can be accessed from anywhere via REST API and web pages built in PowerShell. Schedule tasks and monitor script output with a secure, role-based admin console and end-user portal. Empower your team with a platform that makes PowerShell easy to use and accessible to everyone.
Whether you're a small business or a large enterprise, you will be in good company among the customers using our solutions. With millions of installs, API requests, and scripts executed every month, we help ensure you can make the most of your IT team.










I’m excited to announce that PowerShell Universal has officially joined Devolutions. Through this acquisition we will be able to scale PowerShell Universal while sticking to its core mission of enabling IT administrators and scripters to build accessible, powerful and secure automation solutions. PowerShell Universal was born from the open-source community and that vision remains unchanged. Devolutions shares these same values and will continue to focus on openness, collaboration and long-term sustainability of the platform.
PowerShell Universal v5.6 PowerShell Universal v5.6 is now available. This release includes a number of new features and improvements. Below you’ll find some highlighted features as well as a roadmap for the next couple of releases. You can download the latest version of PowerShell Universal from our download page. For a full list of changes, please visit our changelog page. As always, we recommend testing this version in a development environment before upgrading your production environment.
GitHub Copilot is an AI helper that can run in an editor like Visual Studio Code. It provides code completion as well as chat capabilities to analyze and generate code. GitHub Copilot also supports Agent mode, which allows for communication with additional tools to perform actions on your behalf. In this post, we’ll look at how to expose PowerShell Universal as a tool for GitHub Copilot to perform actions. Model Context Protocol (MCP) The Model Context Protocol, or MCP, is a standard for exposing tools to AI agents like Copilot.